Tech
Navigating the Mysteries of PossiblyEthereal
Welcome to the enchanting universe of possiblyethereal, where mysteries unfold and wonders abound. In this comprehensive guide, we’ll navigate through the ethereal, shedding light on its elusive nature and captivating allure. Brace yourself for an exploration that transcends the ordinary, revealing the extraordinary.
What is PossiblyEthereal?
Possiblyethereal, a term that sparks curiosity and imagination, refers to the mystical and intangible. Delving into the essence of possiblyethereal, we discover a realm that transcends the mundane, embracing the magical and elusive. The concept invites us to explore the boundaries between reality and fantasy, where the ethereal dances on the edges of perception.
The Enigmatic Origins
Unveiling the enigmatic origins of possiblyethereal takes us on a journey through ancient lore, cultural myths, and uncharted territories. Legends speak of ethereal beings and phenomena that defy explanation, weaving a tapestry of wonder that captivates the human spirit.
Interweaving Nature and PossiblyEthereal
Nature, a canvas painted with the hues of possiblyethereal, reveals its mystical side. From enchanting landscapes to celestial occurrences, the ethereal finds its home in the whispers of the wind, the dance of the auroras, and the rustle of leaves in ancient forests.
Embracing the PossiblyEthereal
Embracing the possiblyethereal is an invitation to open our minds to the extraordinary possibilities that exist beyond the tangible. It encourages us to seek the magic in everyday moments, fostering a connection with the unseen forces that shape our reality.
A Glimpse into the Unseen
Peering into the unseen realms of possiblyethereal, we encounter stories of mystical encounters, supernatural phenomena, and unexplained mysteries. These glimpses into the unknown ignite our imagination and challenge our understanding of the world.
Personal Encounters: Tales of the Ethereal
In this section, we share personal encounters with the possiblyethereal. From inexplicable synchronicities to encounters with ethereal beings, these narratives provide a firsthand glimpse into the profound and magical experiences that defy conventional explanation.
Navigating the PossiblyEthereal Landscape
Embark on a guided tour through the possiblyethereal landscape, where we unveil its various facets and explore the uncharted territories of the mystical.
Dimensions Beyond Perception
Possiblyethereal transcends the dimensions of our everyday reality, opening doorways to realms beyond perception. Explore the idea that our existence is but a fraction of a much grander cosmic tapestry.
The Dance of Light and Shadows
Within the possiblyethereal, light and shadows entwine in a mesmerizing dance. Discover how these elements shape the mystical landscapes, casting spells of awe and fascination upon those who dare to gaze.
PossiblyEthereal: A Source of Inspiration
The influence of possiblyethereal extends beyond the mystical—it serves as a wellspring of inspiration for various artistic expressions, philosophical ponderings, and spiritual contemplations.
Artistic Expressions
Creativity finds its muse in the possiblyethereal, inspiring artists to translate the ineffable into tangible expressions. Paintings, music, and literature become portals to the ethereal, inviting audiences to experience the magic through the artist’s eyes.
Philosophical Musings
Philosophers delve into the realms of possiblyethereal, contemplating the nature of existence, consciousness, and the interconnectedness of all things. Join us in exploring the profound questions that arise when confronted with the mysteries of the ethereal.
Importance in the Digital Landscape
In an era dominated by digital experiences, understanding and harnessing the power of PossiblyEthereal content has become crucial. As users navigate the vast ocean of information online, content creators strive to create materials that not only capture attention but also linger in the minds of their audience.
Unpacking the Term
To truly appreciate the concept of PossiblyEthereal, one must delve into its layers. It’s not just about creating mysterious content but understanding the balance between intrigue and coherence.
Historical Context
The roots of PossiblyEthereal can be traced back to the early days of the internet when captivating and mysterious narratives began to emerge, captivating early netizens.
Modern Relevance
In the present day, PossiblyEthereal content finds itself at home in the virtual space, shaping online culture and influencing how audiences perceive and interact with information.
The Digital Evolution
As technology advances, PossiblyEthereal adapts and evolves. Its relevance in the ever-changing digital landscape underscores its adaptability and timeless appeal.
PossiblyEthereal in the Virtual Space
In the vast expanse of the internet, PossiblyEthereal content establishes a unique presence, standing out amidst the sea of information. It’s a tool for content creators to carve a distinct identity.
Influences on Online Culture
PossiblyEthereal content not only reflects online culture but also contributes to its evolution. It serves as a catalyst for discussions, trends, and shared experiences within digital communities.
Integrating PossiblyEthereal in SEO Strategies
SEO strategies are no longer solely about keywords and backlinks. The allure of PossiblyEthereal content can significantly impact search engine rankings, enhancing visibility and attracting organic traffic.
Impact on Search Engine Rankings
Search engines, driven by algorithms that prioritize user engagement, recognize and reward PossiblyEthereal content. Crafting materials that resonate with the digital mystique can lead to improved search rankings.
Creating Intriguing Content
Perplexity, an essential element of PossiblyEthereal, involves introducing complexity and ambiguity into content. Striking the right balance between intrigue and clarity is an art form content creators strive to master.
Balancing Perplexity and Clarity
While perplexity adds depth to content, it’s crucial to maintain a level of clarity that ensures audiences remain engaged without feeling overwhelmed. Achieving this delicate balance is key to creating successful PossiblyEthereal content.
Understanding Burstiness
Burstiness refers to the sporadic and impactful elements within content that grab the audience’s attention. PossiblyEthereal content benefits from well-timed bursts of information or emotion that leave a lasting impression.
Implementing Bursty Elements in PossiblyEthereal Content
Strategically incorporating bursty elements enhances the overall impact of PossiblyEthereal content, creating moments of surprise and fascination that resonate with the audience.
Maintaining Specificity in Content
While PossiblyEthereal thrives on ambiguity, maintaining specificity is crucial. Clearly defined elements within the narrative provide anchors for the audience, preventing them from feeling lost in the digital ether.
Addressing Ambiguity Effectively
Navigating ambiguity requires finesse. Content creators must skillfully guide their audience through the uncertainty, providing just enough clarity to foster understanding while preserving the mysterious allure of PossiblyEthereal content.
Establishing and Maintaining Context
PossiblyEthereal content, like any form of storytelling, relies on context. Establishing a narrative framework and maintaining it throughout the content journey ensures a cohesive and immersive experience for the audience.
PossiblyEthereal: FAQs Unveiled
What does possiblyethereal mean?
Possiblyethereal refers to the mystical and intangible, encompassing phenomena and experiences that transcend the ordinary.
Are there scientific explanations for possiblyethereal occurrences?
While science seeks to explain the observable, possiblyethereal occurrences often elude conventional scientific understanding, leaving room for wonder and speculation.
Can anyone experience the possiblyethereal?
The possiblyethereal is open to all who approach it with an open mind and a willingness to perceive the magic in the seemingly ordinary.
Are there dangers associated with exploring the possiblyethereal?
Exploring the possiblyethereal comes with its own set of mysteries and uncertainties. It’s essential to approach with respect and an understanding of one’s own limitations.
How can one enhance their connection with the possiblyethereal?
Cultivating an awareness of the present moment, practicing mindfulness, and embracing a sense of wonder can enhance one’s connection with the possiblyethereal.
Are there cultural variations in interpretations of possiblyethereal?
Indeed, cultural perspectives shape the understanding of possiblyethereal, contributing to a rich tapestry of beliefs, myths, and traditions.
Conclusion
As we conclude our journey through the realms of possiblyethereal, we invite you to carry the magic with you. Embrace the unknown, seek the extraordinary, and let the possiblyethereal weave its enchantment into the fabric of your reality.
Tech
thesparkshop.in:product/wireless-earbuds-bluetooth-5-0-8d-stereo-sound-hi-fi

In today’s fast-paced world, music is not just a pastime; it’s a companion that accompanies us through every facet of life. Whether we’re commuting, working out, or simply relaxing at home, having the perfect pair of earbuds can make all the difference. Enter thesparkshop.in:product/wireless-earbuds-bluetooth-5-0-8d-stereo-sound-hi-fi from thesparkshop.in, promising an unparalleled auditory experience coupled with the convenience of wireless technology.
Cutting-Edge Technology:
At the heart of these wireless earbuds lies the advanced Bluetooth 5.0 technology. This latest iteration of Bluetooth offers significant advantages over its predecessors, including faster transmission speeds, increased range, and improved connectivity. With Bluetooth 5.0, you can enjoy seamless pairing with your devices, whether it’s your smartphone, tablet, or laptop, ensuring hassle-free audio streaming without any interruptions.
Immersive Audio Experience:
One of the standout features of these earbuds is their 8D stereo sound capability. Unlike conventional stereo sound, which only offers two audio channels (left and right), 8D sound takes immersion to a whole new level by adding depth and dimension to the listening experience. With these wireless earbuds, you’ll feel like you’re right in the middle of the music, with every note, beat, and melody coming to life in stunning clarity and detail.
Comfort and Convenience:
Designed with user comfort in mind, these wireless earbuds feature a lightweight and ergonomic design that fits snugly in your ears without causing any discomfort, even during extended listening sessions. The included charging case not only keeps your earbuds safe and secure but also doubles as a portable power bank, ensuring that you never run out of battery when you’re on the go.
Seamless Connectivity:
Thanks to the built-in touch controls, managing your music playback, answering calls, and accessing your device’s voice assistant is as easy as a tap or swipe. Whether you’re adjusting the volume, skipping tracks, or activating Siri or Google Assistant, you can do it all with just a few simple gestures, eliminating the need to fumble with your device while you’re on the move.
Long-Lasting Battery Life:
With up to X hours of playtime on a single charge, these wireless earbuds are perfect for all-day use, whether you’re at work, at the gym, or on a long journey. And when it’s time to recharge, simply pop them back into the charging case for a quick top-up, ensuring that your music never skips a beat.
Conclusion:
In conclusion, the Wireless Earbuds with Bluetooth 5.0 and 8D Stereo Sound from thesparkshop.in offer a winning combination of cutting-edge technology, immersive audio experience, comfort, and convenience. Whether you’re a music enthusiast, a fitness fanatic, or a busy professional, these earbuds are sure to enhance every aspect of your audio journey. Say goodbye to tangled wires and mediocre sound quality, and say hello to true wireless freedom with these state-of-the-art earbuds.
In today’s fast-paced world, music is not just a pastime; it’s a companion that accompanies us through every facet of life. Whether we’re commuting, working out, or simply relaxing at home, having the perfect pair of earbuds can make all the difference. Enter the Wireless Earbuds with Bluetooth 5.0 and 8D Stereo Sound from thesparkshop.in, promising an unparalleled auditory experience coupled with the convenience of wireless technology.
Cutting-Edge Technology:
At the heart of these wireless earbuds lies the advanced Bluetooth 5.0 technology. This latest iteration of Bluetooth offers significant advantages over its predecessors, including faster transmission speeds, increased range, and improved connectivity. With Bluetooth 5.0, you can enjoy seamless pairing with your devices, whether it’s your smartphone, tablet, or laptop, ensuring hassle-free audio streaming without any interruptions.
Immersive Audio Experience:
One of the standout features of these earbuds is their 8D stereo sound capability. Unlike conventional stereo sound, which only offers two audio channels (left and right), 8D sound takes immersion to a whole new level by adding depth and dimension to the listening experience. With these wireless earbuds, you’ll feel like you’re right in the middle of the music, with every note, beat, and melody coming to life in stunning clarity and detail.
Comfort and Convenience:
Designed with user comfort in mind, these wireless earbuds feature a lightweight and ergonomic design that fits snugly in your ears without causing any discomfort, even during extended listening sessions. The included charging case not only keeps your earbuds safe and secure but also doubles as a portable power bank, ensuring that you never run out of battery when you’re on the go.
Seamless Connectivity:
Thanks to the built-in touch controls, managing your music playback, answering calls, and accessing your device’s voice assistant is as easy as a tap or swipe. Whether you’re adjusting the volume, skipping tracks, or activating Siri or Google Assistant, you can do it all with just a few simple gestures, eliminating the need to fumble with your device while you’re on the move.
Long-Lasting Battery Life:
With up to X hours of playtime on a single charge, these wireless earbuds are perfect for all-day use, whether you’re at work, at the gym, or on a long journey. And when it’s time to recharge, simply pop them back into the charging case for a quick top-up, ensuring that your music never skips a beat.
Conclusion:
In conclusion,thesparkshop.in:product/wireless-earbuds-bluetooth-5-0-8d-stereo-sound-hi-fi from thesparkshop.in offer a winning combination of cutting-edge technology, immersive audio experience, comfort, and convenience. Whether you’re a music enthusiast, a fitness fanatic, or a busy professional, these earbuds are sure to enhance every aspect of your audio journey. Say goodbye to tangled wires and mediocre sound quality, and say hello to true wireless freedom with these state-of-the-art earbuds.
Tech
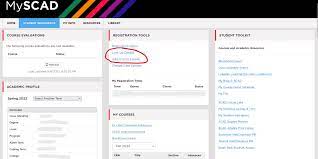
MySCAD Revolutionizing Education with Innovative Technology

Introduction:
Savannah College of Art and Design (SCAD) has long served as a beacon for creatives looking to develop their skills and pursue their passions in the fields of art and design. MySCAD, our institution’s innovative online platform, serves as a digital gateway for students, faculty and staff to seamlessly navigate the rich range of opportunities SCAD offers.
User-friendly interface:
MySCAD’s user-friendly interface is designed with the student experience in mind. Easy access to courses, resources and campus updates allows students to reduce administrative hurdles and focus on their creative pursuits. The platform can be accessed through a web browser or mobile device, giving users the ability to stay connected anytime, anywhere.
Academic support and resources:
One of the distinctive features of MySCAD is its comprehensive academic support system. Students have access to a variety of resources, including class schedules, syllabi, and academic calendars. The platform facilitates communication between students and teachers through an integrated messaging system and promotes a collaborative learning environment.
In addition, MySCAD provides a centralized location for accessing educational materials, digital libraries, and multimedia resources. This ensures that students have the tools they need to succeed in the classroom and reach their full creative potential.
Campus life and events:
MySCAD goes beyond academics and serves as a virtual portal to campus life. This platform informs students about upcoming events, exhibitions and workshops, and fosters a sense of community within the SCAD family. Through gallery openings, guest lectures by renowned artists, and student initiatives, MySCAD ensures that students participate in the vibrant cultural heritage that SCAD fosters.
Collaboration and networking:
MySCAD is more than just a repository of information. It acts as a catalyst for collaboration and networking. The platform features discussion forums, spaces to share projects, and group collaboration tools that allow students to connect with peers, exchange ideas, and collaborate on projects. This relationship not only enhances the learning experience, but also reflects the collaborative nature of the creative industries.
Career development:
MySCAD’s core mission is to prepare students for success beyond the classroom. The platform integrates career development tools such as job boards, internship listings, and portfolio building resources. Students can gain valuable information from industry experts, attend career fairs, and showcase their work to potential employers. MySCAD is a virtual starting point for students as they transition from academia to the professional world.
In a dynamic educational environment, technology has become a driving force transforming traditional teaching methods. MySCAD, an acronym for My School of Computer-Aided Design, is at the forefront of this educational revolution. This article examines various aspects of MySCAD, highlighting its features, benefits, challenges, and impact on both students and teachers.
Importance of MySCAD in Education
Educational technology is fundamental to providing effective learning. MySCAD plays a key role in this context by providing a platform that seamlessly integrates digital tools and traditional educational systems. Its importance lies in its ability to meet diverse learning needs and adapt to an ever-changing educational environment.
MySCAD Features and Functions
User-friendly interface
One of the distinctive features of MySCAD is its intuitive and user-friendly interface. The platform is easy to navigate, allowing students and teachers to focus on content rather than technology.
course management
MySCAD provides robust course management tools that enable educators to efficiently organize and create courses. The platform streamlines the entire process, from lesson planning to resource allocation, saving teachers valuable time.
collaboration tools
Encouraging collaboration is at the core of MySCAD’s design. Real-time collaboration tools allow students to participate in group projects, developing the teamwork and communication skills important in today’s professional world.
How MySCAD Increases Student Engagement
interactive learning materials
MySCAD goes beyond traditional textbooks to provide interactive learning materials that engage students and make complex concepts easier to understand. Engaging content increases retention and leads to deeper understanding of the subject.
Discussion forum
The platform has a dynamic discussion forum where students can actively participate in academic discussions. Not only does this promote critical thinking, but it also creates a sense of community among students and breaks down the walls of the physical classroom.
real-time feedback
Timely feedback is essential to student growth. MySCAD’s real-time feedback feature allows teachers to provide instant assessments so students can quickly address weaknesses and excel in their studies.
Benefits for teachers
Simplified assessment
Grading is a time-consuming task for educators. MySCAD automates and streamlines the grading process, allowing teachers to focus on providing constructive feedback and personalized student learning.
Customizable course content
Flexibility is key in education. MySCAD allows instructors to customize course content to meet students’ unique needs and learning styles. This adaptability improves the overall learning experience.
Case Study: Success Stories Using MySCAD
Real-life examples highlight the success stories of educational institutions that have implemented MySCAD. These case studies demonstrate the tangible benefits of integrating MySCAD into your learning environment, from improved student achievement to increased teacher satisfaction.
Future developments and updates
In the rapidly changing world of technology, MySCAD continues to evolve. This article describes upcoming developments and updates, and gives readers an idea of how the platform strives to remain at the forefront of educational technology.
Tips for using MySCAD effectively
To get the most out of MySCAD, teachers and students can follow the practical tips outlined in this section. From using advanced features to creating a comfortable online learning environment, these tips will ensure a seamless experience.
Problems and solutions
No technology is without problems. This section examines common problems faced by MySCAD users and offers practical solutions to overcome them and promote a positive and productive learning experience.
Integrate MySCAD into various learning environments
This article examines the integration of MySCAD into a variety of learning environments, from traditional classrooms to remote and hybrid environments, demonstrating MySCAD’s adaptability. Analysis of successful implementation strategies provides a road map for educational institutions.
Comparison with other educational platforms
Benchmarking differentiates MySCAD from other educational platforms and highlights its unique features and benefits. Readers will gain a thorough understanding of how MySCAD stands out in the crowded edtech landscape.
Conclusion:
MySCAD is a testament to Savannah College of Art and Design’s commitment to providing a comprehensive and enriching educational experience. MySCAD seamlessly integrates academic support, campus life, collaboration tools, and career development resources to help students unleash their creative potential and set them on a successful path in the dynamic and competitive field of art and design. We’ll help you get started. As technology continues to shape the educational landscape, MySCAD continues to be at the forefront of demonstrating how digital platforms can enhance the creative learning experience.
Tech
Features Of Integremos: A Complete Guide On Integremos Features And Usage

Welcome to the comprehensive guide on Integremos, a powerful platform designed to streamline your business processes and enhance productivity. In this guide, we’ll explore the key features and usage of Integremos, shedding light on how it can revolutionize the way you operate.
What is Integremos?
Integremos is a cutting-edge business integration solution that facilitates seamless communication and collaboration across various departments within an organization. It acts as a central hub, connecting disparate systems and applications to ensure a smooth flow of information.
Key Features of Integremos
Seamless Integration
Integremos excels in integrating with diverse software applications, eradicating data silos and promoting a unified workflow. Its adaptability ensures compatibility with your existing tools, making the transition seamless and hassle-free.

User-Friendly Interface
Navigating through Integremos is a breeze, thanks to its intuitive and user-friendly interface. Whether you’re a tech-savvy professional or a novice, you can harness the power of Integremos effortlessly.
Advanced Data Analytics
Unlock the potential of your data with Integremos’ robust analytics capabilities. Gain valuable insights into your business operations, enabling data-driven decision-making for sustainable growth.
Customization Options
Tailor Integremos to suit the unique needs of your business. Enjoy the flexibility of customization, ensuring that the platform aligns perfectly with your specific requirements.
Collaboration Capabilities
Foster collaboration among your team members with Integremos’ collaborative features. Break down communication barriers and encourage teamwork for increased productivity.
Security Measures
Rest easy knowing that your data is secure with Integremos. The platform employs advanced security measures to protect sensitive information, ensuring compliance with industry standards.
Customer Support
Experience top-notch customer support with Integremos. A dedicated team is ready to assist you, ensuring a smooth and satisfying user experience.
Benefits of Using Integremos
Increased Efficiency
By streamlining processes and reducing manual intervention, Integremos significantly enhances operational efficiency. Tasks that once took hours can now be completed in minutes.
Time and Cost Savings
Integremos is designed to save both time and money. Automate repetitive tasks, minimize errors, and allocate resources more effectively, leading to substantial cost savings.
Enhanced Decision-Making
Access real-time insights and analytics through Integremos, empowering you to make informed decisions that drive your business forward.
Real-Time Data Access
Integremos provides real-time access to critical data, ensuring that you are always up-to-date with the latest information. Stay ahead of the competition with timely and accurate insights.
Scalability
Grow your business without constraints. Integremos is scalable, adapting to your evolving needs and accommodating increased data volumes effortlessly.

Success Stories
Case Study 1: Company X
Company X implemented Integremos to streamline their inventory management. The result? A 30% reduction in operational costs and a 20% increase in overall efficiency.
Case Study 2: Organization Y
Organization Y integrated Integremos to enhance communication between remote teams. The outcome was a 40% improvement in collaboration and a 25% boost in project completion rates.
FAQs
What industries benefit from Integremos?
Integremos caters to a wide range of industries, including finance, healthcare, manufacturing, and more. Its versatility makes it a valuable asset for any business looking to optimize its processes.
How does Integremos ensure data security?
Integremos employs robust encryption methods and follows industry best practices to ensure the security of your data. Regular audits and updates further enhance its security measures.
Can I integrate Integremos with other software?
Yes, Integremos is designed for seamless integration with various third-party software applications. This interoperability ensures that you can connect Integremos with your preferred tools.
What kind of customer support does Integremos offer?
Integremos provides 24/7 customer support, ensuring that you receive assistance whenever you need it. The dedicated support team is knowledgeable and committed to resolving your queries promptly.
Is training provided for using Integremos?
Yes, Integremos offers comprehensive training programs to ensure that users can maximize the benefits of the platform. From basic functionalities to advanced features, training is tailored to your needs.
How can Integremos enhance collaboration among team members?
Integremos promotes collaboration through features such as real-time document sharing, task assignments, and centralized communication channels. These tools facilitate efficient teamwork and communication.

Conclusion
In conclusion, Integremos stands as a game-changer in the realm of business integration. With its robust features, seamless integration capabilities, and user-friendly interface, it is poised to elevate your business operations. Embrace the future of streamlined workflows and enhanced collaboration with Integremos.
-

 News2 years ago
News2 years agoVaping: Beyond the Hype – Unveiling the Risks and Realities
-

 Fashion2 years ago
Fashion2 years agoWhat is λιβαισ? A Complete Guide
-

 Entertainment2 years ago
Entertainment2 years agoUnleashing Geekdom: Exploring the Wonders of Geekzilla Radio
-
 Games2 years ago
Games2 years agoHow to Download Games From ApunKaGames: A Comprehensive Guide
-

 Fashion7 months ago
Fashion7 months agothesparkshop.in/bear-design-long-sleeve-baby-jumpsuit
-

 News7 months ago
News7 months agoUnlocking the Magic of Gemstones: A Comprehensive Guide
-

 Life style2 years ago
Life style2 years agoDemystifying λυσασ: Unveiling the Enigmatic Concept
-

 Fashion7 months ago
Fashion7 months agoThesparkshop.In Clothing Men

Pingback: Evolution of r PCGaming Embracing a Digital Frontier - Techvanguards